How to secure phpMyAdmin on Ubuntu 15.04
phpMyAdmin Apache Ubuntu Security Authentication Authorization
Introduction
When it come to cyber security it should be taken very seriously. Most commonly used web applications such as WordPress store all your information including passwords on a MySQL database. phpMyAdmin is an excellent way to manage theses information stored on MySQL databases. However because of its ubiquity, phpMyAdmin it is a popular target for attackers.
In this tutorial, we will go over how to secure phpMyAdmin to prevent unauthorised access.
Use a Strong Password
This may seem obvious but most attackers get access to phpMyAdmin using an attack method know as brute force attack. Brute force attacks consist of systematically checking all possible passwords until the correct one is found. Use a password that doesn't have any dictionary words and include numbers and symbols on your password.
Change phpMyAdmin Path
By default phpMyAdmin web interface is accessed using /phpmyadmin/ path. We can change this path to a secret path, by doing this only users who know this path can access phpMyAdmin interface.
We need to edit this file to change web interface path for phpMyAdmin /etc/apache2/conf-enabled/phpmyadmin.conf, you can open this file using your preferred text editor, I will be using nano for this tutorial:
sudo nano /etc/apache2/conf-enabled/phpmyadmin.conf
You should see a line that looks like this on the top of the page.
Alias /phpmyadmin /usr/share/phpmyadmin
This line will forward all incoming traffic to /phpmyadmin/ to /usr/share/phpmyadmin, where phpMyAdmin files are located. We can edit the /phpmyadmin to any path you like, for this example, I will use the path /secret. It should look like this once edited.
Alias /secret /usr/share/phpmyadmin
Now save the file and restart apache to load changes we have made by running this command:
sudo service apache2 restart
You can now access phpMyAdmin web interface using your public Ip address or domain name followed by the secret path.
Apache Authentication
In addition to changing the path, we can use Apache authentication and authorization module to require users to log in using a set username and password before they can log in to phpMyAdmin.
First, we need to install apache2-utils package using apt-get package repository. You can run the following command to install this package:
sudo apt-get install apache2-utils
Now we can create the user and password that will be used to authenticate with Apache to access phpMyAdmin.
sudo htpasswd -c /usr/share/phpmyadmin/.htpasswd user
You will be asked to enter the password for the user and confirm it. This command will create the .htpasswd file in /usr/share/phpmyadmin/ directory which will include our username and encrypted password.
If you would like to add additional users to an existing htpasswd file, you have to run the command without the -c flag, for example:
sudo htpasswd /usr/share/phpmyadmin/.htpasswd seconduser
We need to edit the /etc/apache2/conf-enabled/phpmyadmin.conf file and tell it to use the htpasswd file we created. Again, I will be using nano to edit the file, but you can use your preferred text editor.
sudo nano /etc/apache2/conf-enabled/phpmyadmin.conf
Add the lines in red to your configuration file.
<Directory /usr/share/phpmyadmin>
Options FollowSymLinks
DirectoryIndex index.php
AuthType Basic
AuthName "Restricted Files"
AuthUserFile /usr/share/phpmyadmin/.htpasswd
Require valid-user
Save the file and close out of nano once you have added the lines in red.
We are almost done, we need to restart Apache to implement the changes we have made. You can restart Apache by running this command:
sudo service apache2 restart
Now you should see a message similar to this when you go to your phpMyAdmin web interface.
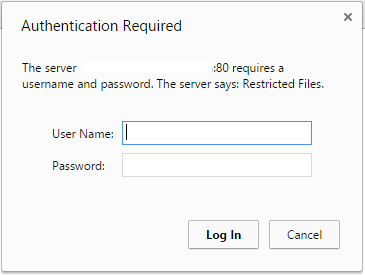
Type the username and password that we created to continue to phpMyAdmin.
Conclusion
Above methods will add additional layers of security to phpMyAdmin making it difficult for attackers to get into your phpMyAdmin. However more and more vulnerabilities are found each day when it comes to servers, you should always be running the latest versions of programs to protect yourself from theses vulnerabilities.

Comments
Add comment